FAQs on implementing NABL directive on QR codes - Part 1
- Rajesh Soundararajan
- Sep 20, 2021
- 4 min read
Most asked Questions
Scanning and Verification
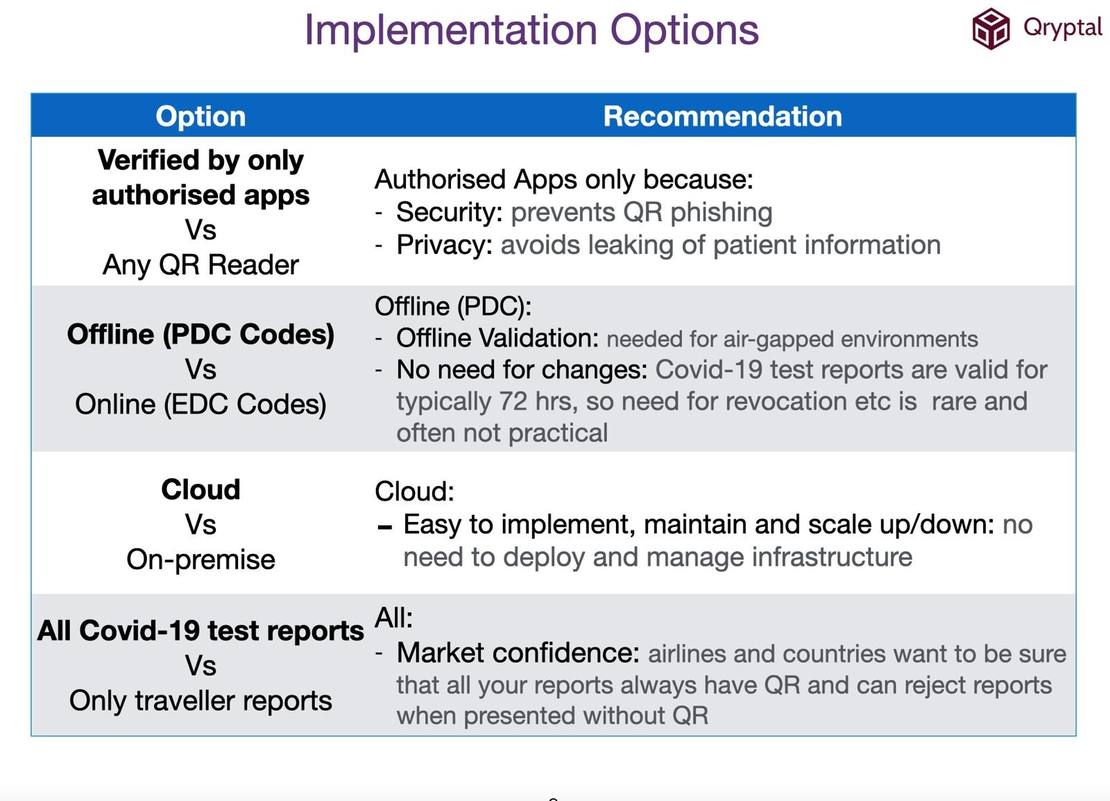
1. Can I use any QR scanner, or is there a specific scanner for validation?
Yes, you can use any QR scanner for scanning the QR code. For example, the newer Android and iPhone cameras already have the QR code scanner built in. Most phone cameras can be used to scan the QR code. Qryptal secure QR codes will be set up to be URL-based to enable this feature. This same secure digitally-signed QR code content is used as part of the URL
2. What is the QR code scanning technology behind this?
When you scan the QR code (in the context of NABL), it is essentially an URL (text). However, with the Qryptal secure code solution, the URL contains secured digitally signed information in the form of a code. The digitally signing algorithm uses industry-standard cryptography based on private and public key pairs. The QR Code content is digitally signed using a private key that belongs and identifies your company. The PDF report file is encrypted and stored encrypted with the decryption keys embedded securely in the QR. At verification, the content is verified using the corresponding public key. The QR content and document are then shown only if the QR has not been tampered with. Hence, secure QR solutions like what Qryptal offers delivers the highest levels of security. Furthermore, NABL’s requirement is primarily about having your report available on an URL for easy verification. So in effect, the Qryptal solution helps meet the NABL requirement and deliver significantly higher levels of security.
Technology Overview
3. What are the system requirements for installing the QR code-based document security for NABL?
It is just a simple three-step process.
a. The laboratory prepares the test /lab report in a pdf format.
b. You can then log into the system, upload the report to the QR code generation system.
c. You can download the final report embedded with a QR code.
4. What is a public key? How are public keys used in the solution to provide security?
Every time the QR code is generated, it gets signed by your private key, and the public key is present on your verification domain (verify.yourcompany.com).
Qryptal enables the end-end delivery of the solution by integrating the creation, embedding, and verification seamlessly. When a third-party verifier scans the QR code, it goes to the designated ‘verification URL’ that you have setup -. Therefore, the public key distribution becomes imperative. For example, in the case of vaccination certificates, border control might not have Internet access. At that time, they take the public key and store it in their system or use the dedicated app to validate on their own. So if your verification domain is used, the public key is already a part of it for anybody who wants to verify.
5. If you have the public key, can anyone access the report?
Even when the public key is available, the only way to access the report is by scanning the QR code. The information is not stored anywhere where it can be accessed by public key alone. When someone scans the QR code, the public key is used only to verify the digitally signed information securely embedded in the QR to determine that it has not been tampered with. Once that is determined, the information in the PDF file is decrypted, and presented to the user. So just with the public key alone, no one has access to any information.
On-Premise vs. Cloud
6. Can we save the QR code report on our internal server (after generation) instead of storing it on your server? Can we implement this solution without the internet on a local server?
Technologically, yes. Qryptal solution can help you generate the QR code locally and also store it on the local system. However, the NABL requirement specifies that you will need to have the document available online for verification with the URL. Due to this mandate, once the QR codes document is generated, you will need to make it available for access on the internet. The storage of the document as an encrypted blob can be on your own cloud storage or on Qryptal’s cloud storage.
You may also like -
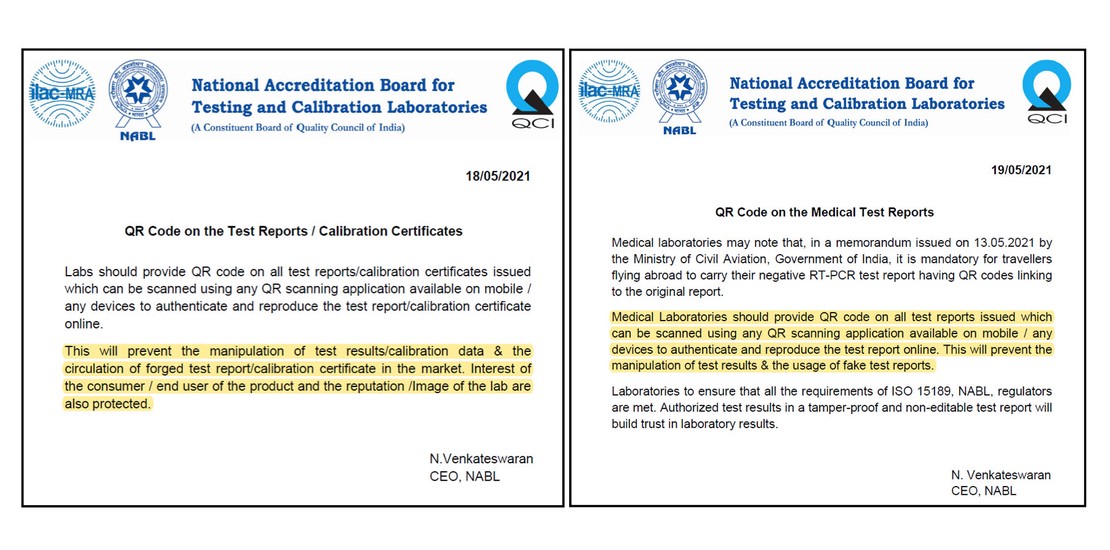
- Why NABL Mandated QR Codes for Document Security
- Secure QR Codes for Laboratory Reports
- How can Labs and Testing organizations implement and integrate NABL Mandate on QR Codes ?
- India’s Tryst with Fake RT-PCR reports and why regular QR doesn’t help