QR Codes in 2022 – The Ultimate Guide to Secure QR Code Creation
- Rajesh Soundararajan
- Mar 29, 2022
- 3 min read
Create Tamper-Proof Secure QR Codes in 5 Simple Steps
In part 1 of this series - QR Codes in 2022 – A double-edged sword? -we discussed the rapid growth of QR codes worldwide and their increasing use in various industries. Now, we’ll delve deeper into the essential steps to create secure, tamper-proof QR codes and maintain safety while using them.
The story so far
“QR Code”, short for Quick Response Code, has been utilized for over 25 years across numerous industries. QR codes are two-dimensional barcodes encoding information such as website addresses, contact information, and more. With the widespread adoption of smartphones capable of reading QR codes, their popularity has skyrocketed. Unfortunately, the ease of QR code creation has also led to a surge in fraud, making it imperative to generate secure QR codes at the source.
Creation of QR Code that is Secure
Although numerous QR code generators are available, not all provide the necessary security to prevent fraud. Therefore, it’s crucial to know how to create tamper-proof and secure QR codes.
How to create a Secure, Encrypted QR Code
Implementing a secure, encrypted QR code is an effective and easy solution for document security. Placing these QR codes on documents makes them tamper-proof and verifiable by a third party without database reliance and ensures privacy.
The 5-step process for creating a tamper-proof Secure QR code
Step 1: Choose a reputable secure QR code service provider that offers an end-to-end solution for generating secure, encrypted QR codes and validating the documents they’re placed on.
Step 2: Generate and embed the encrypted QR code using a manual or automated process with API integration, depending on your system and use case requirements.
Step 3: Ensure the encrypted codes are digitally signed with the private key of the issuing organization, making them tamper-proof and exclusive to authorized entities.
Step 4: Distribute the document with a secure, encrypted QR code in electronic or physical format, catering to various environments and connectivity situations.
Step 5: Scan the encrypted QR code on the document using an approved validation app or web validation mechanism, both of which carry the corresponding public key for verification.
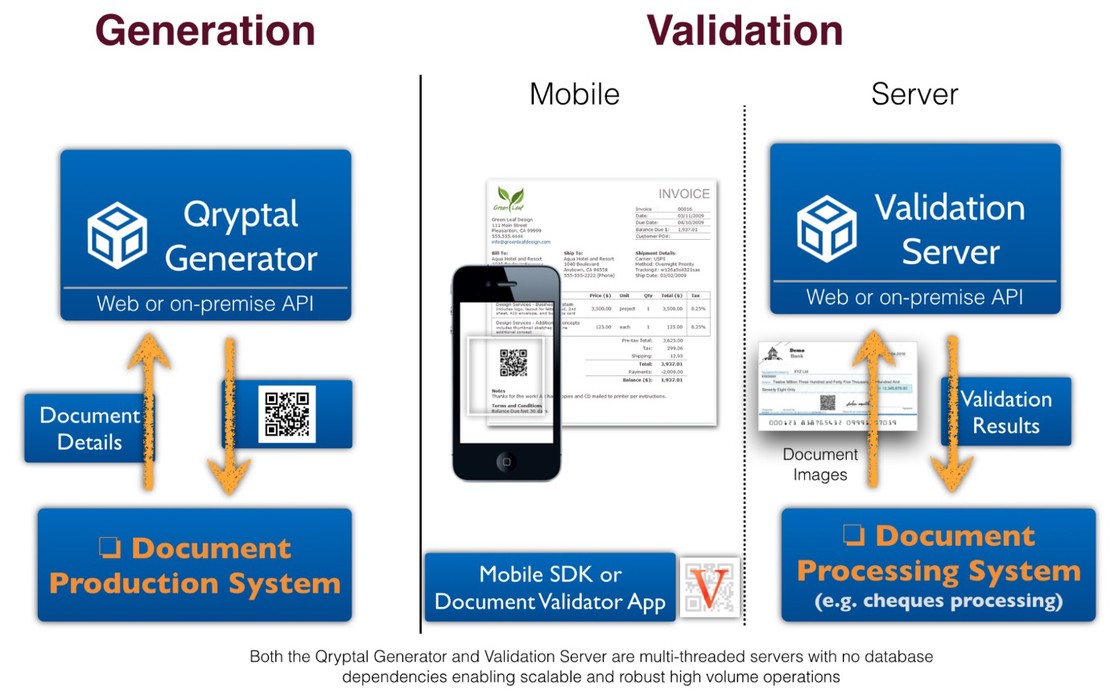
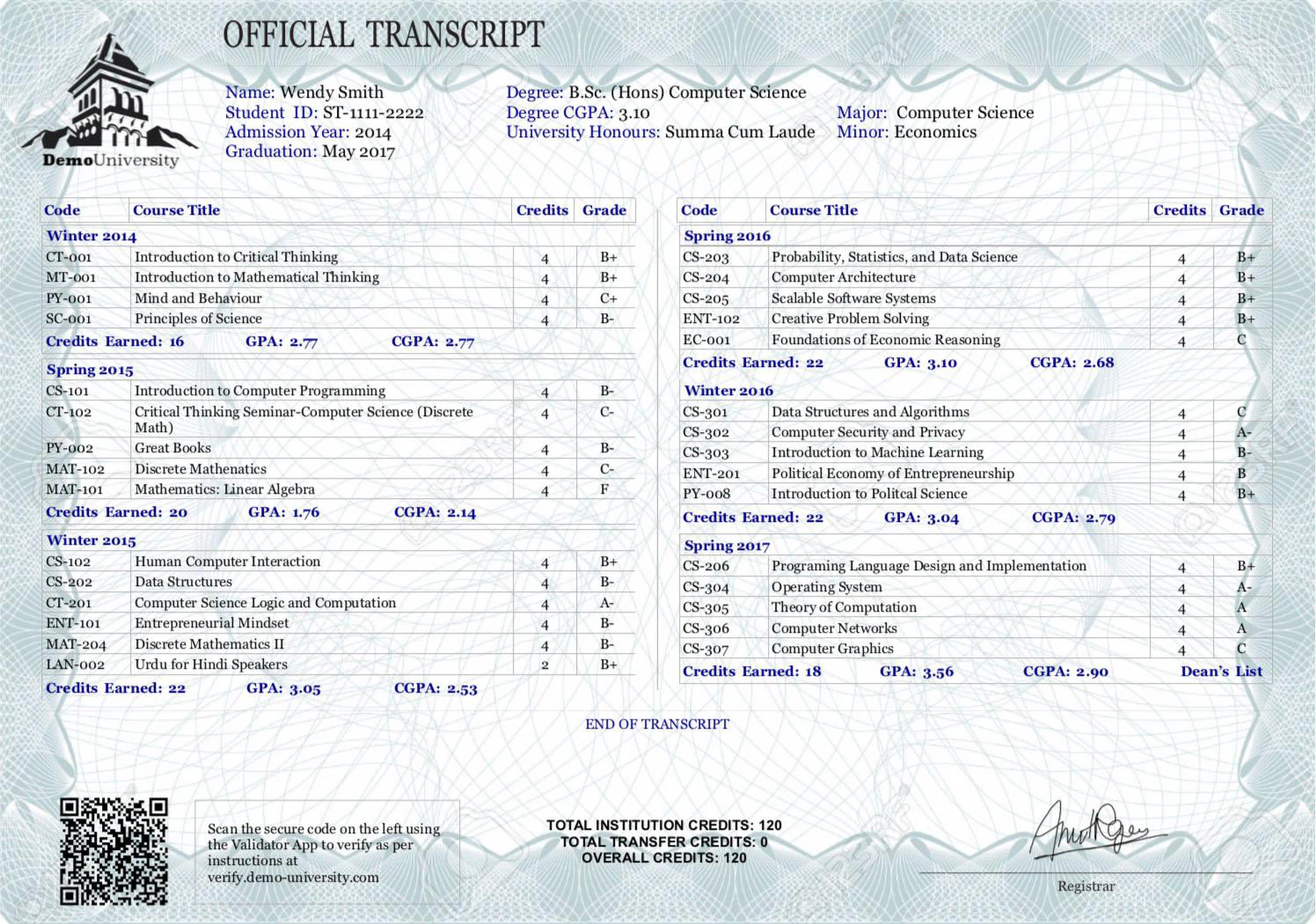
Schematic Representation
Secure QR Code use cases (with images)
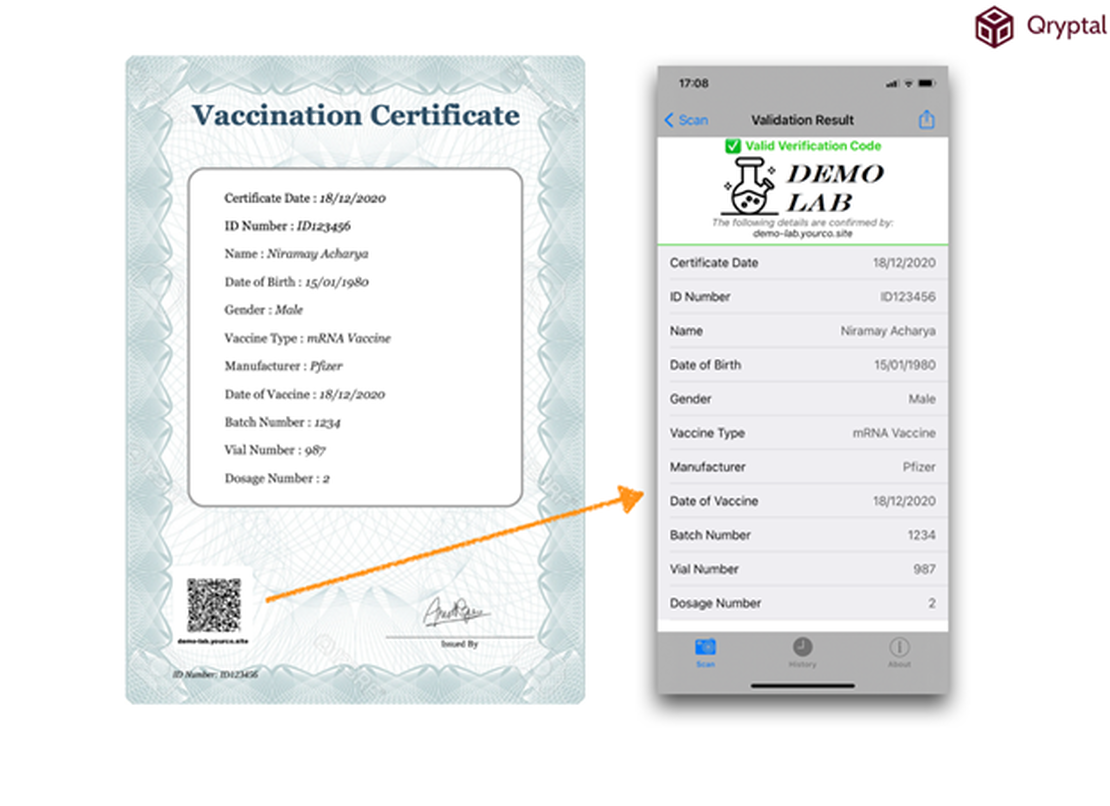
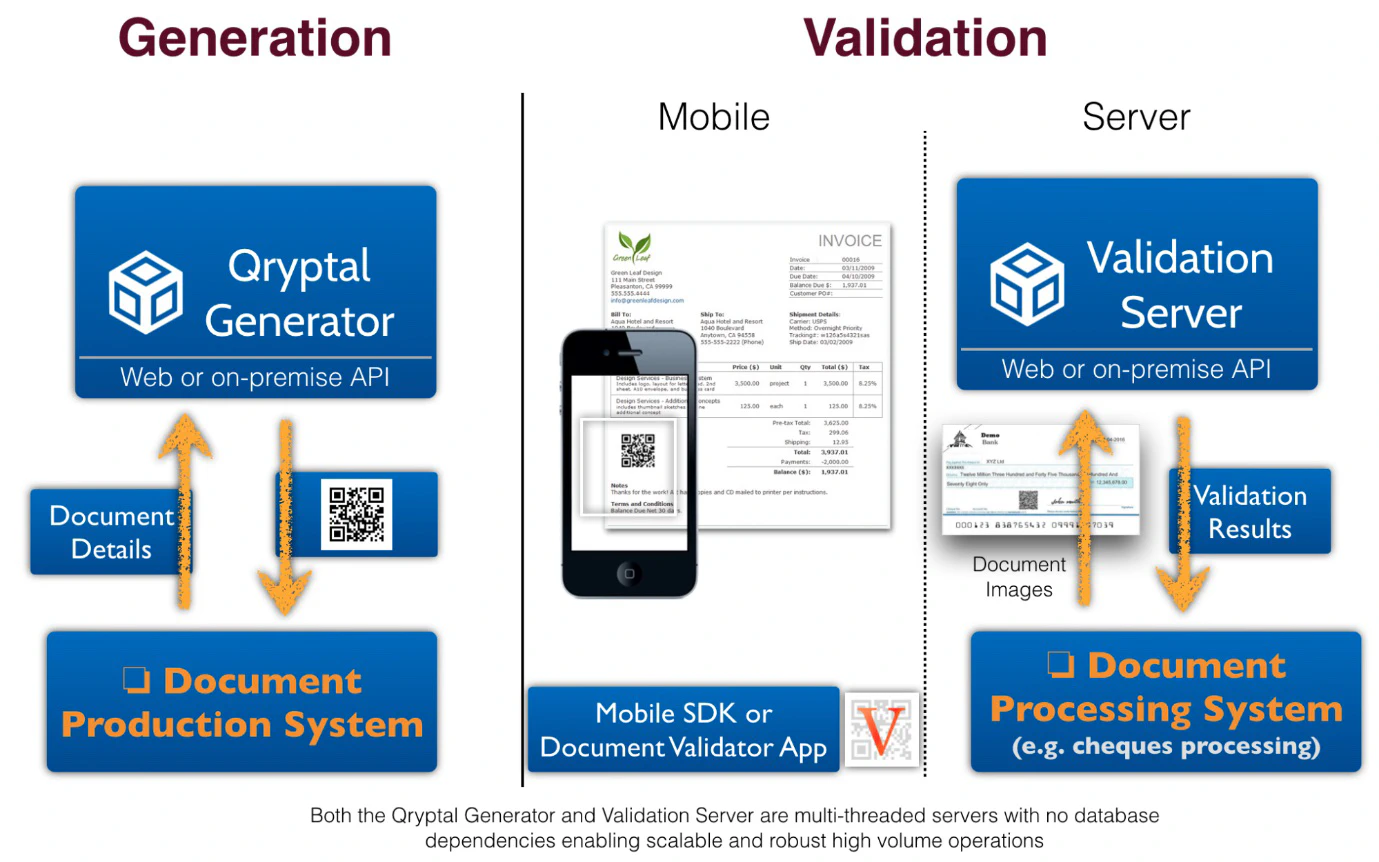
Covid Vaccination Certificate
A Secure QR code embedded in the vaccination certificate allows verifiers to check a person’s vaccination status and relevant details easily. Vaccinated individuals can download a PDF for their records and present it to authorities when needed. A sample is given here:
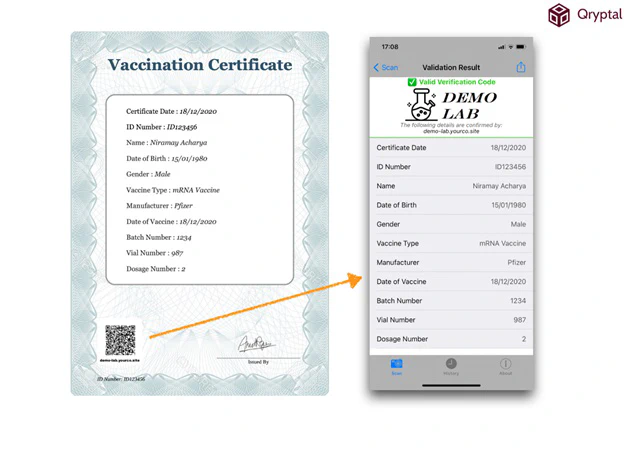
University Transcripts
Secure QR codes offer several advantages for document security, such as seamless security, tamper-proofing, easy generation, affordable integration, and ease of verification. A university transcript with a secure QR code may look like this:
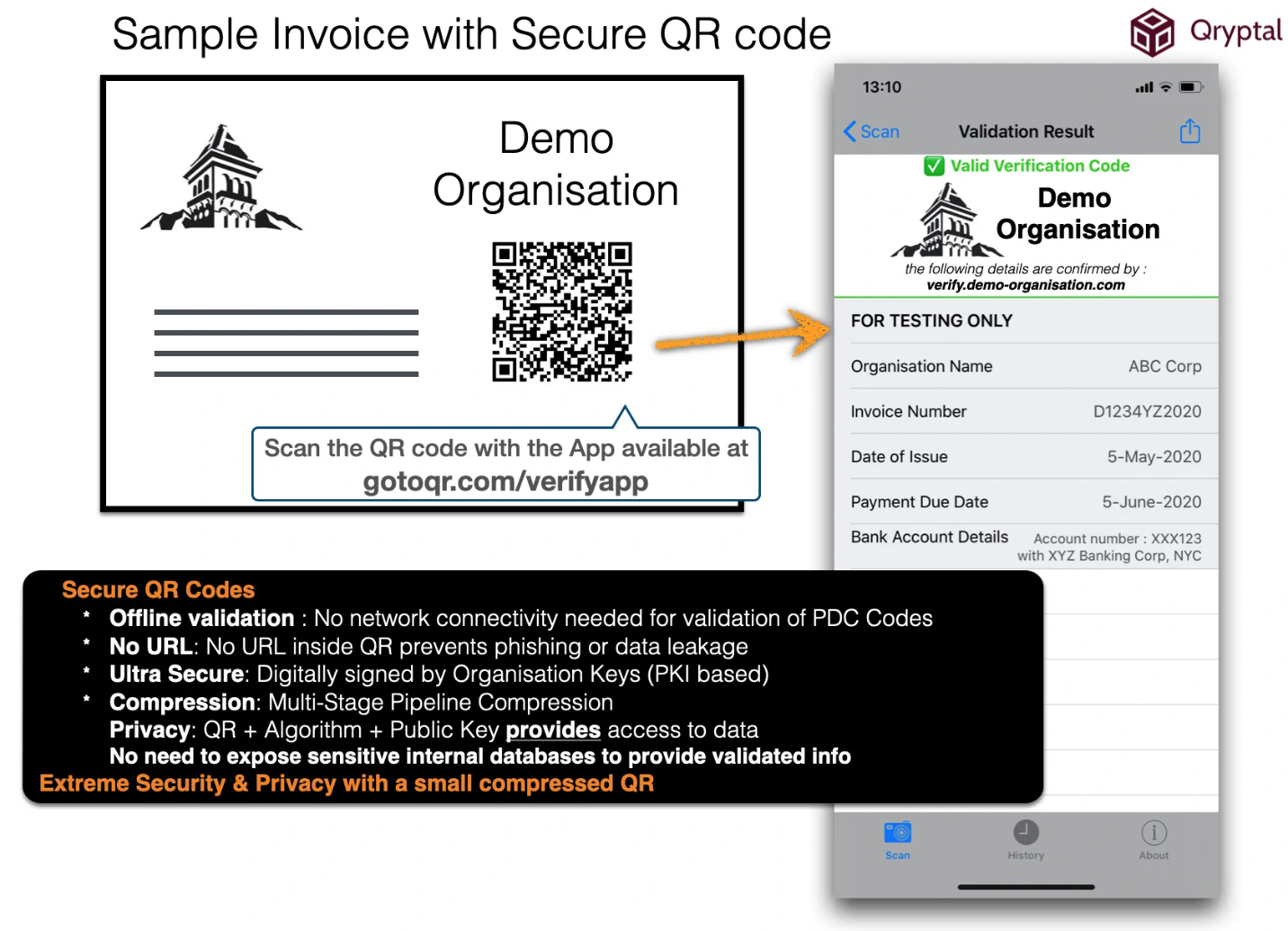
Secure QR Based Invoice
Integrating a secure QR code generation system with your ERP can enhance trust and facilitate information capture for further processing.
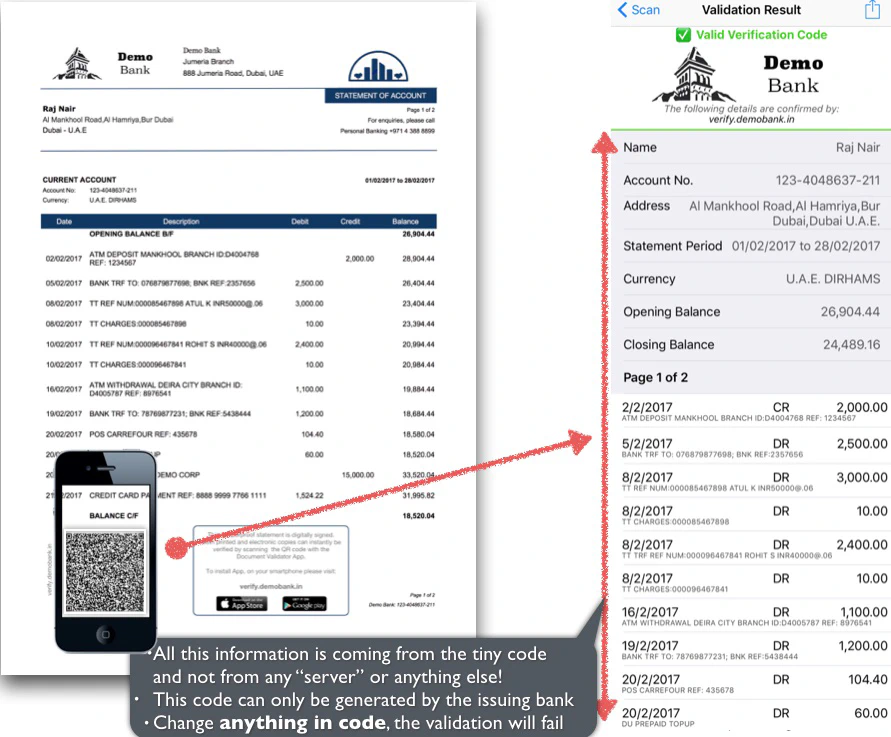
Bank Account Statement
Bank account statements can be made tamper-proof and easily verifiable using Secure QR Codes. These QR codes capture account-related data at the time of statement generation and are signed by the issuing bank’s private key, ensuring security and preventing forgery.
In summary, while QR code generation is simple, it’s essential to follow the necessary steps to create and use Secure QR codes, ensuring document security and enhancing trust and reliability among users.
You may also like -
- COVID-19 Vaccination Certificates - Top 10 points
- Did we tell you about preventing forged University Transcripts
- COVID times have brought Fake Invoice Scams into focus like never before
- 3 reasons Why Bank Account Statements should be secured using Qryptal QR Code technology